The Foundation of a Reliable Network for Texas Businesses
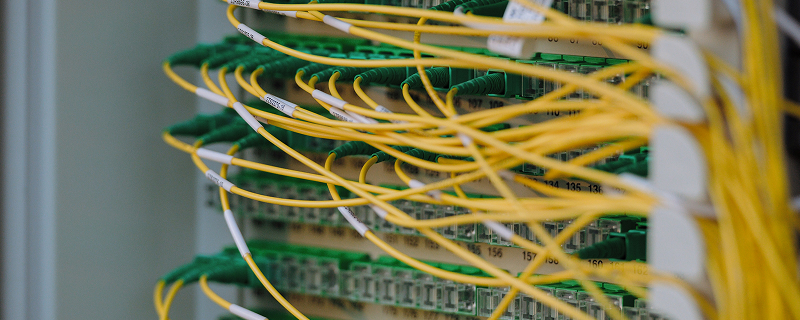
In today's interconnected business environment, a robust and well-organized network infrastructure is paramount. Structured cabling is the backbone of this infrastructure, providing a standardized and flexible cabling system that supports all your communication needs—from voice and data to video and security. At LD3 Technology, we specialize in designing, installing, and maintaining high-performance structured cabling systems that ensure optimal network performance, scalability, and reliability for businesses across Texas, including Houston, San Antonio, Dallas, Austin, and Fort Worth.
What We Do For You
Prevent data breaches and financial losses before they happen.
Ensure compliance with industry security regulations and standards.
Protect sensitive customer and company data from threats.
Give you peace of mind with constant protection.
Keep your business running without costly cyber disruptions.
How We Keep You secure
Our cybersecurity solutions protect your business from evolving threats, preventing breaches, downtime, and data loss. With proactive security measures, continuous monitoring, and advanced threat defense, we safeguard your operations, ensuring compliance and resilience. Stay secure, productive, and confident with our comprehensive cybersecurity approach.
24/7 Threat Detection
We continuously monitor your network for suspicious activity, identifying and stopping cyber threats before they cause harm. Real-time analysis and rapid response ensure your business stays protected around the clock.
Zero-Trust Framework
We implement strict access controls, verifying every user and device before granting access. This approach minimizes insider threats and unauthorized entry, ensuring only the right people access your critical data and systems.
Multi-Layered Defense Systems
Our security approach combines firewalls, endpoint protection, email filtering, and access controls to create a robust defense. By layering security measures, we minimize risk and block attacks before they reach critical systems.
Employee Security Awareness Training
Human error is a major cybersecurity risk. We provide ongoing training to educate employees on phishing, social engineering, and safe digital practices, reducing vulnerabilities and strengthening your overall security posture.
Our Structured Cabling Solutions for Texas Businesses
We offer comprehensive structured cabling solutions tailored to your specific requirements, ensuring a future-proof network foundation:
Design & Planning
Our expert team works with you to design a cabling infrastructure that meets your current and future needs, adhering to industry standards and best practices.
Site Assessment: Thorough evaluation of your facility to determine optimal cable routing and equipment placement.
System Design: Creation of detailed cabling blueprints, including cable types, pathways, and termination points.
Scalability Planning: Designing a system that can easily accommodate future expansions and technological advancements.
Installation & Implementation
Our certified technicians ensure a professional and efficient installation process, minimizing disruption to your operations.
Copper Cabling (Cat5e, Cat6, Cat6a): Installation of high-quality copper cabling for reliable data and voice transmission.
Fiber Optic Cabling: Deployment of fiber optic solutions for high-bandwidth applications and long-distance connectivity.
Cable Management: Implementing organized and labeled cabling systems for easy identification, troubleshooting, and maintenance.
Testing & Certification: Comprehensive testing of all installed cables to ensure compliance with performance standards and provide certification reports.
Maintenance & Support
We provide ongoing support and maintenance to ensure the continued performance and longevity of your structured cabling system.
Troubleshooting & Repair: Prompt identification and resolution of cabling issues to minimize downtime.
Adds, Moves, and Changes: Flexible support for modifications and expansions to your existing cabling infrastructure.
System Upgrades: Recommendations and implementation of upgrades to keep your cabling system current with evolving technology.
Rapid Incident Response
Quick action minimizes damage. Our expert team rapidly identifies, contains, and resolves security incidents, restoring systems efficiently. With structured response plans, we help your business recover quickly while preventing future breaches.
Compliance-Driven Security
Meeting compliance standards is crucial. We provide risk assessments, security audits, and policy implementation to ensure your business aligns with regulations, protecting sensitive data and avoiding fines or legal issues.
Why Choose LD3 Technology for Structured Cabling in Texas?
Certified Expertise: Our technicians are highly trained and certified in the latest structured cabling standards and technologies.
Reliability & Performance: We build cabling systems that deliver consistent, high- speed performance, reducing network bottlenecks and downtime.
Future-Proof Solutions: Our designs anticipate future technological needs, ensuring your infrastructure can support emerging applications.
Organized & Efficient: We pride ourselves on clean, organized installations that simplify management and reduce operational costs.
Comprehensive Support: From initial design to ongoing maintenance, we provide end-to-end support for your cabling infrastructure.

FAQs About Our Cybersecurity Services
What are the biggest cybersecurity threats businesses face today?
Businesses face ransomware, phishing attacks, insider threats, weak passwords, unsecured devices, and data breaches. Cybercriminals constantly evolve their tactics, making proactive security measures essential to protect sensitive information and prevent financial and operational damage.
How often should businesses update their cybersecurity measures?
Cybersecurity should be reviewed continuously, with major updates at least annually. Regular software patches, employee training, and security assessments help keep defenses strong against emerging threats and evolving attack methods.
What is multi-layered security, and why is it important?
Multi-layered security combines different protective measures—firewalls, endpoint protection, encryption, and access controls—to defend against cyber threats. No single solution is foolproof, so multiple layers reduce risk and block attacks from different angles.
How can businesses protect against phishing attacks?
Employee awareness training is crucial. Additionally, businesses should use email filtering, multi-factor authentication (MFA), and endpoint security tools to detect and block phishing attempts before they compromise sensitive data.
What is the dark web, and why does it matter for cybersecurity?
The dark web is an underground part of the internet where cybercriminals sell stolen data. Monitoring the dark web for exposed credentials can help businesses prevent breaches before stolen information is exploited.
How does zero-trust security improve cybersecurity?
Zero-trust security requires continuous verification of users, devices, and applications before granting access. This prevents unauthorized access, limits potential breaches, and ensures only trusted users interact with sensitive systems.
What should businesses do after a data breach?
Immediately contain the breach, identify affected systems, notify relevant parties, and implement stronger security measures. Conduct a post-incident review to prevent future breaches and improve security resilience.
Why is compliance important in cybersecurity?
Compliance ensures businesses follow industry regulations designed to protect sensitive data. Failing to comply can lead to fines, legal consequences, and reputational damage, making it essential to maintain secure practices.
How can businesses secure remote employees?
Use VPNs, enforce multi-factor authentication, require strong passwords, and implement endpoint security solutions. Regular training ensures employees recognize cyber threats and follow best security practices when working remotely.
How does cybersecurity impact business continuity?
A strong cybersecurity strategy prevents disruptions from cyberattacks, protecting data and operations. Without proper security, businesses risk downtime, financial loss, and reputational damage that can severely impact long-term success.
Build a Strong Network Foundation in Texas
Invest in a reliable and scalable network infrastructure with LD3 Technology's structured cabling services. Contact us today for a consultation and let us help you build the foundation for your business's success.
Call (726) 567-9780 today to discuss a custom security plan that meets your needs and keeps your business secure.